Verify™ Privacy
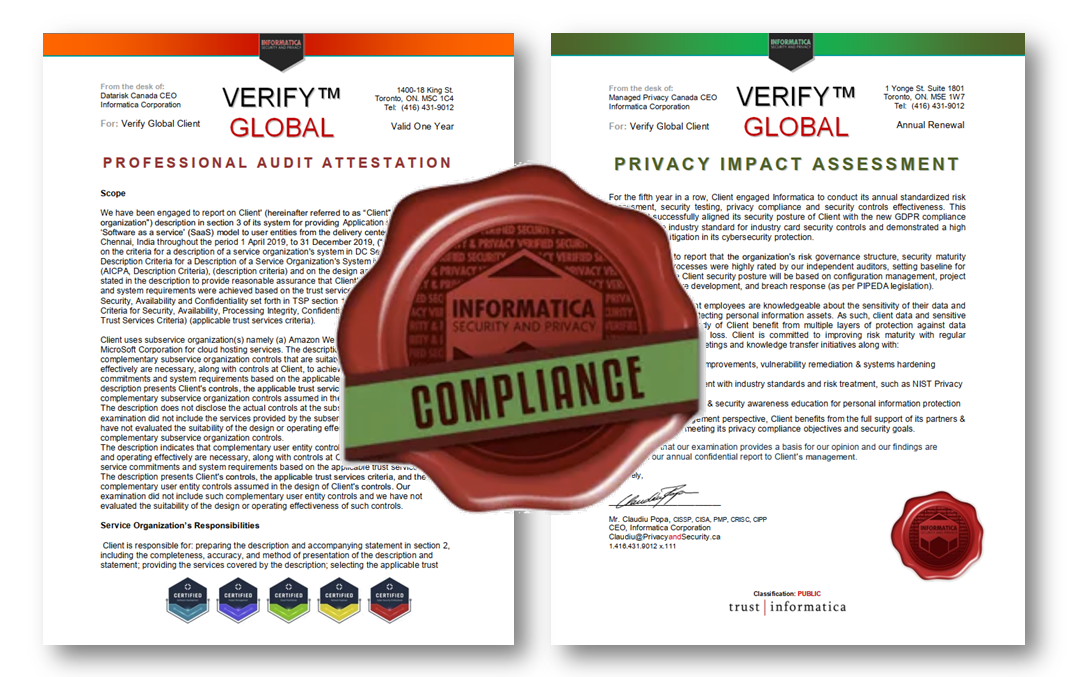
Privacy is law. How is your personal information protection? Get a standardized privacy impact assessment (PIA) report. Use a preliminary analysis (PPIA) to gauge privacy risk.
- Privacy impact assessment (PIA) report
- Preliminary privacy analysis (PPIA)
- Fair Information Practices testing
- GDPR & PIPEDA compliance review
- Statement of Trust™ (upon eligibility)
.svg)